
Don’t let use of personal devices put you at risk.
Personal devices for your in house security? Think again. Friction-less also stands for false positives. Don’t let frustration and lack of consistent security put you at risk. Protect your enterprise and its customers from impersonation, credential theft, and the associated legal ramifications.
Used over 100 million times to protect identity. It works!

BioSig-ID
A patented biometric identity authentication solution that controls access to files and information through MFA in one product. It works on all devices using HTML5.
-
Requires no hardware or software downloads and authenticates users with a four-character password.
-
Blends amazing biometric technology with the password format users are comfortable using.
-
Provides real-time warning of potential data crimes in progress.

BioSight-ID
Used for automatic proctoring of online training and continued education programs.
-
Does not collect any biometric markers and protects the privacy of the user by blurring all images.
-
Works seamlessly with the world’s leading learning management systems (LMSs).
-
Provides complete class and course analytics and guides instructors to find suspicious activity by the student.

BioName-ID
Transforms signatures into digital identity. Prevents use of PNG/JPEG forgeries.
-
Eliminates the need for “wet ink” to attribute the signature to a human.
-
Authenticates signatures through tamper-proof MFA in a single application.

BioTect-ID
Prevents unauthorized access to Windows devices by replacing the device’s native lock screen.
-
Grants access to devices after a successful authentication.
-
Identity credentials can be stored locally to allow temporary use offline.
-
Protects workstations and blocks access to unauthorized users like RDP attacks.
-
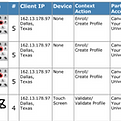
Allows administrators to monitor and change device access ability, reset passwords, and audit illicit access attempts.

BioSafe-ID
A new way to secure eCommerce is coming soon.
Secures online transactions.
-
Prevents “card not present” fraud.
-
Eliminate fraudulent charge-backs.
-
Stops unauthorized credit card transactions.

BioProof-ID
Used for the initial ID verification of an individual.
-
Analyzes the person’s government issued documents and checks the front and back to determine legitimacy of the OCR codes.
-
Stores a user approved “selfie” of the user to compare with photo in the government ID.
-
Provides both verification and authentication of identity.
Bespoke, Analytics and Forensics.
Because we own our technology, it's easy to solve your unique business challenges with a custom solution. We also have advanced analytics and forensics tools to help you make the most out of our advanced cybersecurity solutions.

Data Analytics
Our data analytics suite puts, at your fingertips, the power of time tested AI plus continuous vector analysis. Identify cheaters, impostors and take action with data backing up your decisions.
Data Forensics
Finding a needle in a haystack has never been easier. Our subject matter experts have imbued years of hands on behavioral analysis experience into our AI algorithms.
Custom Solutions
Some customers need a solution beyond those that work "out of the box". We have a proven solutions engineering team ready to solve your most difficult challenges.
